Cellebrite, which is a favourite of law enforcement agencies across the U.S., sells software designed to unlock phones and extract their data. Police frequently use it to gather evidence from seized devices. In the past, the company has received criticism for its willingness to sell to pretty much any government — including repressive regimes around the world. However, despite its mission to compromise phone security everywhere, Cellebrite would appear to have little interest in securing its own software — if you believe the CEO of encrypted chat app Signal.
[related_content first=”1685779″]
In a blog post published Wednesday, Moxie Marlinspike claimed that Cellebrite’s software has atrocious security that can be easily manipulated in a number of pretty astounding ways.
“We were surprised to find that very little care seems to have been given to Cellebrite’s own software security. Industry-standard exploit mitigation defences are missing, and many opportunities for exploitation are present,” Marlinspike writes. “Until Cellebrite is able to accurately repair all vulnerabilities in its software with extremely high confidence, the only remedy a Cellebrite user has is to not scan devices.”
Among many wild claims made in the blog, Marlinspike says that because of security flaws, someone could basically re-write all of the data being collected by Cellebrite’s tools. Hypothetically, a uniquely configured file could be slipped into any app on a targeted device — allowing for the alteration of all of the data that has been or will be collected by Cellebrite’s software.
Such a file could alter data “in any arbitrary way (inserting or removing text, email, photos, contacts, files, or any other data), with no detectable timestamp changes or checksum failures,” the blog states. It continues:
“Given the number of opportunities present, we found that it’s possible to execute arbitrary code on a Cellebrite machine simply by including a specially formatted but otherwise innocuous file in any app on a device that is subsequently plugged into Cellebrite and scanned. There are virtually no limits on the code that can be executed.”
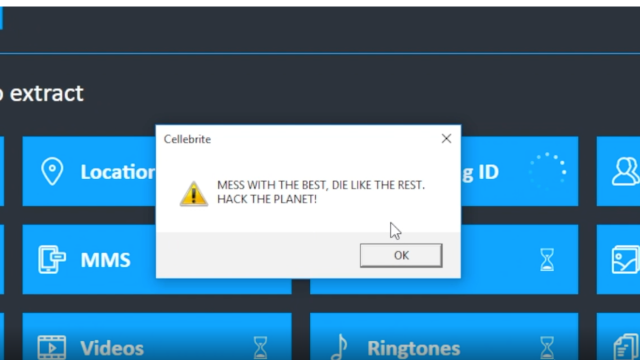
The blog even includes a video, spliced with scenes from the movie Hackers, that shows just how easily Cellebrite’s software can be hijacked:
Our latest blog post explores vulnerabilities and possible Apple copyright violations in Cellebrite’s software:
“Exploiting vulnerabilities in Cellebrite UFED and Physical Analyzer from an app’s perspective”https://t.co/DKgGejPu62 pic.twitter.com/X3ghXrgdfo
— Signal (@signalapp) April 21, 2021
On top of everything, the blog makes another pretty bold claim: code that apparently is the intellectual property of Apple appears within Cellebrite’s software — something Marlinspike says “might present a legal risk for Cellebrite and its users.” In other words, Cellebrite might be selling code that belongs to its biggest adversary.
If all of these disclosures are true, it could have pretty massive ramifications for Cellebrite. If we can assume it’s really this easy for someone to break into the company’s software and drastically alter the data that police are collecting, how certain can law enforcement be that the evidence they are collecting is actually correct? What would the legal ramifications be for the cases that have hinged on Cellebrite’s software, if its security is really so paltry? Anyone who’s been involved in a case that used this software should probably be calling their lawyer right now.
The fact that Marlinspike has very publicly outed these security concerns — and done so without prior disclosure to Cellebrite, as is standard industry practice — could definitely be viewed as a swipe, if not an outright backhanded slap to the face. It’s hard not to read all of this as some sort of retort to Cellebrite’s recent claims that it can crack Signal’s encryption — surely a claim that stuck in Marlinspike’s craw. To top everything off, the Signal CEO actually ends the blog by really making it sound like Signal plans to spam Cellebrite with some sort of malware-adjacent files in the future:
In completely unrelated news, upcoming versions of Signal will be periodically fetching files to place in app storage. These files are never used for anything inside Signal and never interact with Signal software or data, but they look nice, and aesthetics are important in software…We have a few different versions of files that we think are aesthetically pleasing, and will iterate through those slowly over time. There is no other significance to these files.
Shots fired, indeed. We have reached out to Cellebrite for comment and will update this story if we hear back from them.