The fight against ransomware attacks continues, this time on the other side of the Atlantic. Following a two-year investigation, Europol announced this week that it had captured 12 individuals in various criminal organisations who were “wreaking havoc across the world” by launching ransomware attacks on critical infrastructure.
According to Europol, the suspects are believed to have carried out attacks affecting more than 1,800 victims in 71 countries. The group is known for targeting large businesses and is suspected to have been behind an attack on Norsk Hydro — a global aluminium manufacturer based in Norway — in 2019, which forced it to stop production across its factories in two continents. The attack paralysed Norsk Hydro for almost a week and cost the company more than $US50 (A$67) million.
Europol seized more than $US52,000 (A$69,176) in cash from the suspects as well as five luxury vehicles. The agency is currently performing a forensic analysis on the group’s electronic devices to “secure evidence and identify new investigative leads.”
The international sting was coordinated by Europol and Eurojust, the European Union’s agency for criminal justice cooperation, and included authorities from eight different countries, including the U.S. and the UK. It took place in Ukraine and Switzerland on Oct.26, Europol said in a news announcement.
It’s not clear whether the suspects in question have been arrested or charged, with Europol only saying they were “targeted.”
“Most of these suspects are considered high-value targets because they are being investigated in multiple high-profile cases in different jurisdictions,” the agency said.
Each of the cybercriminals had different roles in the criminal organisations. Some were in charge of penetrating the victims’ IT networks and did so using various means, including brute force attacks, SQL injections, stolen credentials, and phishing emails with malicious attachments.
Others got to work once their pals had accessed victims’ IT networks. After the fact, they would deploy malware, such as Trickbot, and other tools to help them stay under the radar and gain further access, Europol explained.
“The criminals would then lay undetected in the compromised systems, sometimes for months, probing for more weaknesses in the IT networks before moving on to monetising the infection by deploying a ransomware,” Europol said, adding: “The effects of the ransomware attacks were devastating as the criminals had had the time to explore the IT networks undetected.”
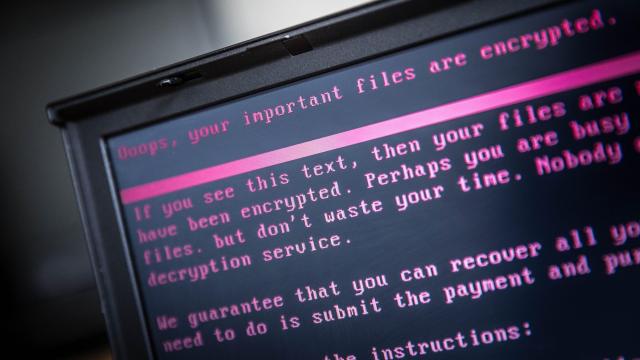
The story then takes a turn and becomes one the majority of us are unfortunately familiar with: The attackers encrypted the victims’ files and then sent a ransom note demanding a payment in bitcoin in exchange for the decryption keys. If the ransom was paid, some suspects were reportedly in charge of laundering the funds through mixing services and cashing out.
Europol did not go into detail about the identity of the group’s victims or why they may have been targeted. Back across the pond, ransomware attacks have also been on the rise, with cybercriminals launching attacks against major IT corporations and crippling infrastructure.