There is nothing more dreadful than seeing your phone drop into the red when you’re lost in a strange place. While it’s always handy to keep a power bank on you, sometimes you just forget to bring it, or keep it fully recharged.
In these scenarios, it’s always tempting to look for some form of publicly accessible charger that you can quickly use to juice up your phone. Problem solved, right?
It may solve your temporary phone battery problem, but you could wind up with a completely different headache if you’re not careful. If the charging cable you’re using is compromised, you could be unknowingly damaging your phone or giving third-parties access to your data.
An attack like this is known as “juice jacking” and involves using the data connectors in most USB cables to access your files, and potentially modify or copy them without you realising.
If you’re about to go travelling and are planning on using public chargers, then you’ll want to use a data blocking USB device to avoid getting juiced jacked.
How does a power cable take my data?
When you’re using your own charger, cable and phone, you’re in full control of the entire transaction, but when you step outside and use any other charger, you’re trusting that it’s not compromised.
When connected, most USB cables transmit power and also allow data to flow through. That’s why you can safely plug your smartphone into your computer to charge while also and shuffling files to and fro.
While public charging station should only provide power, it’s possible to build a system that resembles one of these stations but is actually designed to slurp up the data of connected devices. It’s not a new idea, either – here’s a video from 2012 showing a proof of concept for one of these stations.
How real is the threat of juice jacking?
This is where it gets tricky. While it’s an established concept that doesn’t take much technical nous to implement, documented cases aren’t terribly easy to track down, even if some authorities have highlighted the potential risks, both locally and internationally. There have been some reported cases of it happening in the wild, like this story from India, but it’s not a massive threat in absolute terms.
It’s also a scam that has been at least partially mitigated over the years by the way that both Android and iOS treat connected cables with live data connections.
Plug a modern Android phone into an unknown device and the standard default is to charge only. Typically, users have to select to transfer data or photos through a drop-down menu. Apple’s iOS is even more explicit by asking for “trust” in a connected computer, which is a helpful reminder for those who were only aiming to recharge their phones.
That’s only true of newer devices, however. If you’re using a much older smartphone, it may treat every connection as friendly but then you’d also be some years out of software updates for it to help as well.
This is also not to say that it has never happened or couldn’t. If you’d altered your default phone behaviour for convenience’s sake, or accidentally tapped on the permission dialogue box without realising it, you could potentially put your phone and personal data at risk. Smartphones are a rich source of valuable personal ID, and that means that smartphone operating systems are constantly being prodded for ways to bypass security, including the checks and balances that help to limit this kind of attack.
There’s also potential for social engineering aspects to this – if there was a sign that said you had to click some kind of agreement to charge, how many people might do so in return for “free” power?
Still, it is important to note that this is not a huge risk vector in terms of reported cases and losses, relative to other activities you might engage in with your phone and the precious data within it.
What are my data blocker options?

There’s a wide array of devices that promise to protect you from juice jacking, but they all tend to work in the same way.
Most take the form of either a data-pins-stripped cable (if you’re plugging it directly to a USB-A port) or a dongle that you add to a port or charging cable if you’re not. They’re generally pretty cheap and quite small, so they’re easy to drop into a pocket or purse if you’re heading out and think you might need them.
To be entirely transparent, we haven’t tested these against an attack rig designed for this particular attack, but you could assess them pretty easily by using them plugged into your own PC.
If you’re unable to transfer data even when permitted, or your phone never comes up as a drive on your computer, then they’re doing the job as advertised. If the data still flows regardless, then they’re duds and you’re well within your rights under Australian consumer law to seek a refund pronto.
Which phone data blockers are worth buying?
PortaPow 3rd Gen USB Phone Data Blocker
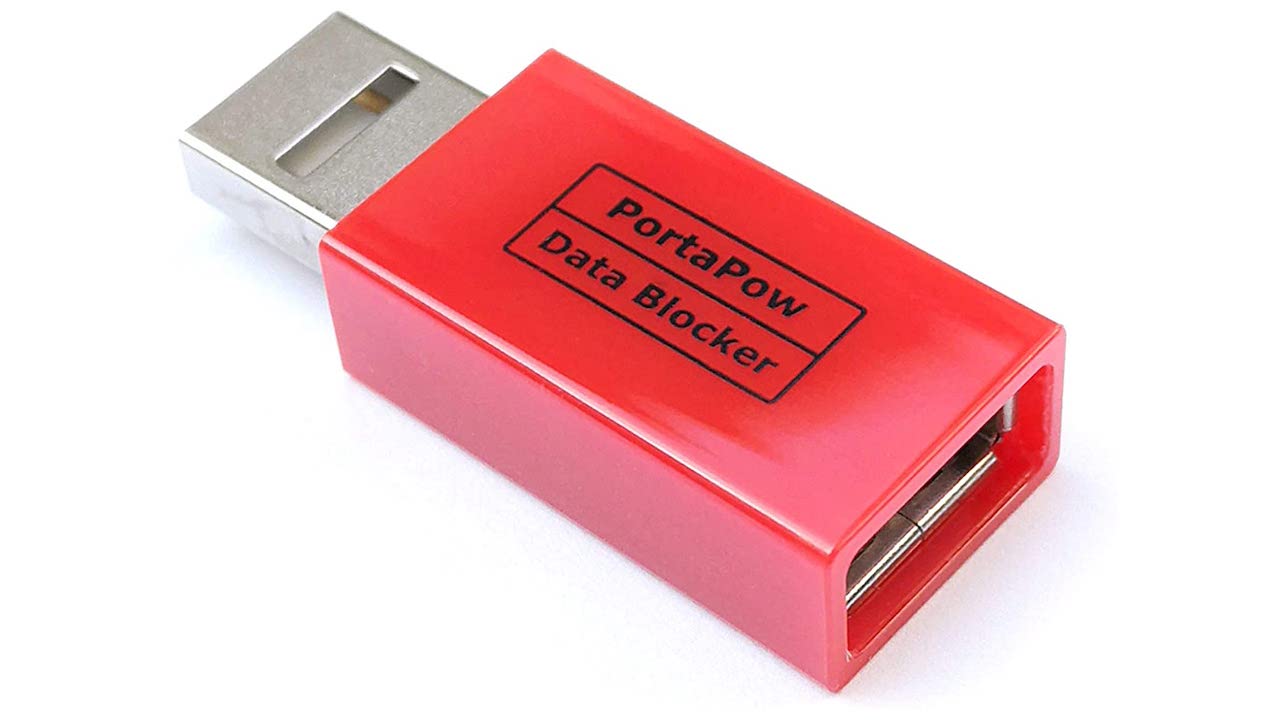
PortaPow phone data blocker claims it’ll even detect your phone type to ensure optimal charging.
Where to buy: Amazon ($21.75) | eBay ($34.45)
Startech USB Phone Data Blocker

Startech makes a range of privacy-centric products for IT and AV professionals, but its USB data blocker is a pretty simple affair that just states that it blocks the data transmission through USB ports – which is exactly what you want out of this kind of gadget.
Where to buy: Dick Smith ($15) | eBay ($15) | mwave ($9.42)
PortaPow USB-C Phone Data Blocker

Juice Jacking isn’t new, but a lot of devices presume you’re connecting to an older USB-A type socket. PortaPow’s USB-C adaptor is a small cable that interconnects to USB-C devices, although the manufacturer notes it’s not suitable for protecting laptops from data theft due to the need for those data channels to remain open while charging.
Where to buy: Amazon ($9.95)
BrexLink Data Blocker

Another USB-A type option, albeit in a less alarming colour that the PortaPow option, and again a simple way to stop the data flow from connected devices if you’re concerned. This pack includes two phone data blockers, which is handy if you’re someone who regularly misplaces small things.
Where to buy: Amazon ($8.99)
