In potentially the largest bank heist on record, an Eastern European hacker ring is stealing or lack thereof) at major financial institutions are so bad, it only takes opening a malware-riddled attachment to jumpstart an international, billion-dollar theft.
Not Exactly Sophisticated
The hacker heist was uncovered by security firm Kaspersky Labs, which categorized the attack as sophisticated. But sophisticated might be overstating it — in fact, this was your basic phishing scam. People actually had to click on a suspicious file to launch the attack. Once somebody clicked on the file, it launched a backdoor exploit called Carbanak, which steals passwords by installing software to record every keystroke that people make — while also taking screenshots. Security journalist Brian Krebs — who first reported the hack back in December — pointed out something important: To gain access to the computers, the hackers are taking a “minimal effort” approach, assuming (rightly) that they can gain entrance just by waiting for someone to casually click open a malware-infested attachment without properly updating their Microsoft Office.
In other words, this wasn’t a zero-day attack; nobody invented a devious new exploit to rob these banks. Worse, the attack was so simple that it could have been prevented if the banks had just installed Microsoft security updates in a timely manner. Unfortunately, as Krebs pointed out, financial firms don’t prioritise digital security. “Most organisations — even many financial institutions — aren’t set up to defeat skilled attackers; their network security is built around ease-of-use, compliance, and/or defeating auditors and regulators,” he wrote.
Many of the systems that large organisations and even financial institutions operate were designed before hacks of this scale became commonplace. But in the aftermath of the massive Sony hack and this current bank heist, companies need to start emphasising security as much as ease of use, or attacks like this will keep happening. It should not take a stray click on a sketchy attachment to open up a security hole that can blossom into a billion-dollar theft, and the fact that it did shows how broken financial digital security is.
“The real vulnerability here is that you have critical internal infrastructure connected to the same machines that people use to read unvetted outside email and browse the web,” Johns Hopkins University computer scientist Matthew Green told me. “There’s no business in the world that can secure a system like this. Until businesses adjust to that reality, these attacks will keep getting worse.”
Anatomy of a Heist
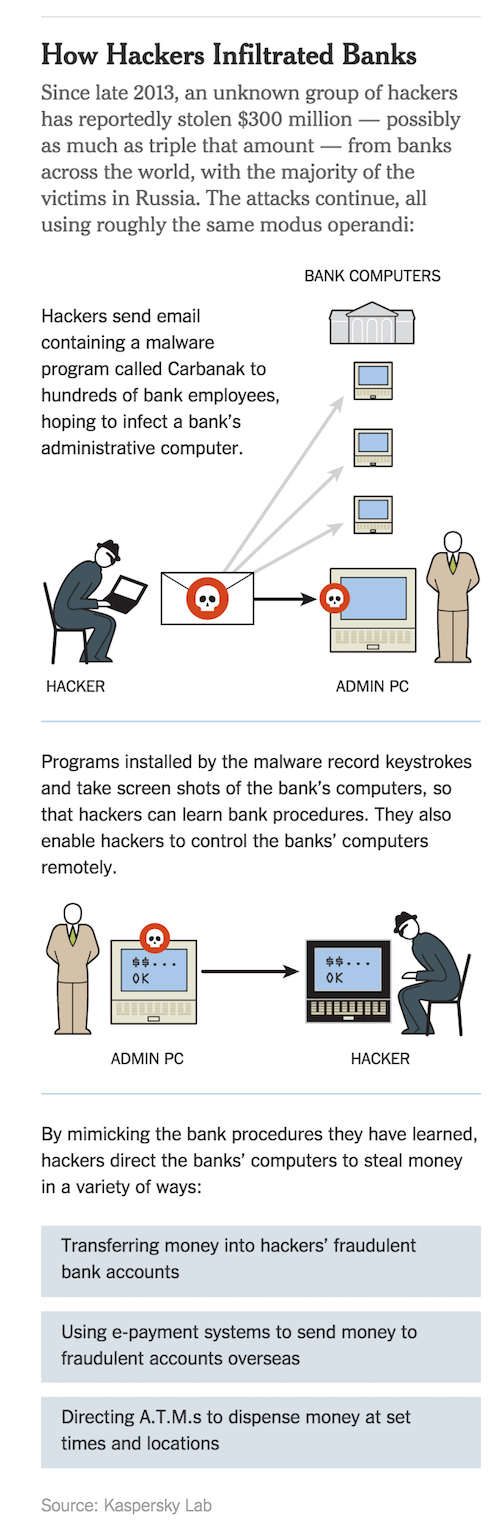
Here’s how it went down: Starting in 2013, internal computers at banks were infected with malware by using standard phishing scams, where hackers hide malware in emails that look legit. The malware used a security hole for Microsoft that had already been patched, on the assumption that some banks wouldn’t have bothered with the security update. Once bank employees clicked on the Microsoft Office attachments within the emails, they were screwed if they hadn’t recently updated their computers.
The hackers were patient, and tracked the computers of bankers, learning how they operated.From there, they’d override ATMs to spew out thousands of dollars to money mules, transfer money directly into their bank accounts, and launch additional phishing attacks on other banks.
Attacking computers using basic phishing tactics is something any greedy script kiddie can manage. While this particular hacking group is pulling some advanced, intelligent maneuvers once they’re already in, it also proved that it’s easy as hell to hack financial institutions. The Kaspersky report cites over 100 banks in 30 countries that have been hacked.
“It’s actually quite common for organisations to run outdated pieces of software because certain tools or applications that were built at some point cannot be easily upgraded,” Malwarebytes security analyst Jérôme Segura told me by email. “For instance, we see the use of older Java or Internet Explorer versions that are required for internal programs to work properly. These systems should be properly sandboxed from the rest of the network because they represent a risk.”
Segura’s recommendations to stop this kind of hacking include exploit mitigation tools, which can stop malware from successfully taking advantage of security holes. At the same time, he recognises that human error is always going to come into play. To combat that, he thinks banks should minimize opportunities for employees to mess things up. “In addition to training, employees should only be given access to parts of the network they really need. Access should also be revoked if no longer required,” he said.
As convenient as it is to check your Gmail while you’re at work in a bank, keeping secure financial processes on the same computer you use to tweet and browse Amazon is irresponsible at this point. Bank security needs to grow up.
[Sources: Kaspersky Labs [Krebs [New York Times]]
Illustration by Tara Jacoby; infographic via New York Times
